top of page
Search
All Posts

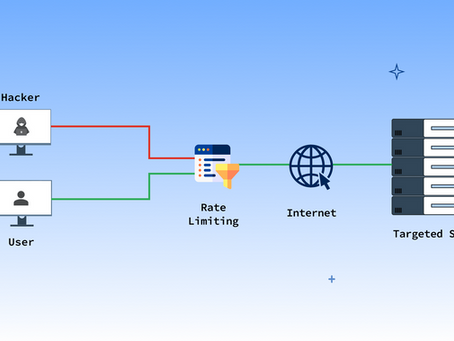
Case Study Distributed Rate Limiting Bypass
During an authentication security assessment, we discovered that the login endpoint's rate limiting was configured with per_edge counting on the CDN/WAF layer. The protection only triggered when concurrent connections exceeded a threshold (~30-50 simultaneous requests). By sending sequential requests—one at a time, waiting for each response—an authenticated attacker could perform unlimited login attempts without triggering any security controls.
erik biserovv
Mar 22 min read


Sensitive Information Disclosure via Public Assets
During a web application security assessment, we discovered that the /app/assets/i18n/en.json endpoint—intended for UI localization—was publicly accessible without authentication. The file contained far more than translation strings: it exposed 133+ internal database field names, entity structures, and business operation labels. A simple curl request returned 40KB of internal system metadata that directly mapped to the application's data
Luchezar Atanasov
Mar 22 min read


CORS Misconfiguration Enabling Cross-Origin Data Theft
During assessment for one of our web clients, we discovered that the server reflected any Origin header value in its CORS response, combined with Access-Control-Allow-Credentials: true. This configuration allowed any external website to make authenticated requests on behalf of logged-in users. An attacker hosting a malicious page could silently fetch sensitive data from the application using the victim's session cookies.
Luchezar Atanasov
Mar 13 min read


Front running mechanism in WEB3
Case Study: The $15 Attack That Could Block a Multi-Chain Protocol Blockchain technologies are different narrative and need to be looked from different angle to bring best value and contribute to safer environment. The Silent Threat Hiding in Plain Sight Centrifuge Protocol had ambitious plans.
erik biserovv
Mar 12 min read


Case study JWT access token with excessively long expiration
Scope: We was given Swagger documentation of company new service APIs for release We found that the application’s JWT access tokens (used for API authentication in most of the APIs) had an unusually long validity period (e.g., 7–30 days) and were not tied to any server‑side revocation or rotation mechanism. Once issued, a stolen token remained valid until its natural expiration, regardless of logout, password change, or role changes. This meant an attacker who obtained a sing
erik biserovv
Mar 12 min read


Case study Broken access control
During audits, we discovered multiple issues in the /internal/profile endpoint, used by the web app to fetch customer details. The endpoint accepted a profile_id parameter and returned full profile data without verifying that the requesting user actually owned that profile. By incrementing or iterating over profile_id values, an authenticated user could enumerate other customers’ records and retrieve PII (name, email, phone, partial address) under certain conditions. Escalati
Luchezar Atanasov
Mar 12 min read


Missinforamation warfare
How a Simple Fact-Checking Extension Became the Front Line Defense Against Modern Information Warfare? We're no longer fighting simple spam or obvious scams. We're fighting an invisible war where the battlefield is your browser, the weapons are pixels and algorithms, and the casualties are truth itself. Situation 1: In February 2022, a deepfake video of Ukrainian President Volodymyr Zelensky surfaced online, showing him supposedly ordering his troops to surrender to Russia
erik biserovv
Nov 6, 20252 min read


Modern AI Warfare
AI-Driven Cybersecurity Risks Could Reshape the Digital Battlefield Published on 21 June 2025 | Security-Program.ai - Editorial Unit As...
erik biserovv
Jun 22, 20253 min read


SentinelDAO: Blockchain as a Guardian of Cybersecurity and Democracy
In a world where disinformation, deepfakes, and digital censorship thrive unchecked, blockchain offers a resilient shield for...
erik biserovv
May 5, 20252 min read


Human element in modern internet
How human element can be saviour in today digital era France, Italy, and current influences: In short, some of the listed threats—such...
erik biserovv
May 3, 20252 min read


OSINT for law enforcement
How to use it ? By leveraging open-source intelligence, law enforcement agencies can gather insights into the networks, hierarchies, and...
erik biserovv
Apr 19, 20252 min read


Open-Source Security: Safeguarding Against Fraud and Hacks
In today's digital age, online security is a critical issue that affects businesses and individuals alike. With the rise of cyber fraud,...
erik biserovv
Apr 6, 20253 min read


Modern internet awareness
In the fast-evolving world , security is a critical concern for users and developers alike. With the rise of Web3 technology,AI and...
erik biserovv
Apr 6, 20252 min read


Emergency Kit
SENTINELDAO: THE DIGITAL FIRST RESPONDER IN A WORLD OF SYNTHETIC CRISES (A News Blog Special Report) By Erik Angelov, Cybersecurity...
erik biserovv
Apr 6, 20253 min read
bottom of page
